Online privacy is of paramount importance these days, given the evolving digital landscape. With several tracking tools now available on the market, data proliferation has become more pronounced than ever before. One such tool is Grabify, which is an IP logger.
The IP logger serves legitimate purposes and offers ethical applications; however, it also raises certain privacy concerns. In this article, we will explore the following sub-heads—
Let us take one sub-topic below one at a time and delve deeper into these topics in brief.
what is grabify?
It is an online tool that allows users to generate links for tracking the IP addresses of users who click on these links. If you click on one such Grabify link, your IP address will be logged. It will reveal details like your location, type of device, and often the ISP, or the internet service provider. People mainly use this IP logger for analytics to track website visitors. However, the objective is much narrower, just for IP logging.
What are IP Grabbers?
These are devices that extract your IP address as you interact with the hyperlinks or any other internet content. You might also encounter them as invisible running scripts on any of the websites that you are browsing. And Grabify is one such IP logger.
How do IP Grabbers work?
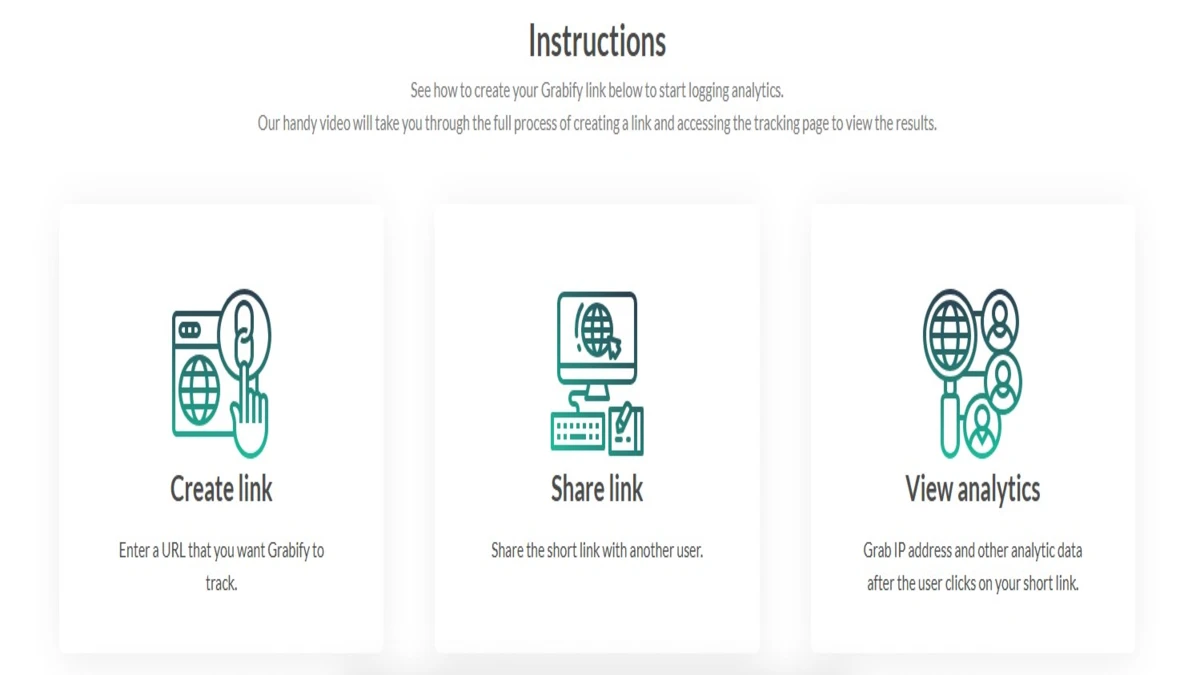
Let us follow these steps below to understand how these IP logging tools work.
- Creating links – A URL is created by the one who intends to attack by grabbing an IP address.
- Distributing the URL – You will find these clickable links in your e-mail, chat applications, and social media platforms.
- Call to Action (Click) – The tool will communicate with the server that is hosting the web content as you click on the link.
- Extracting IP address – As you click the link, your IP address is recorded by the IP grabbing provider.
What are the risks of IP tracking?

IP tracking poses many risks. Let us find out the same related to the Grabify IP logger.
- Targeted attacks – This kind of attack renders your network unstable. The attack comprises using your IP address to launch the Distributed Denial-of-Service or DDoS attacks.
- Geolocation – Your approximate location is revealed, thereby compromising your privacy.
- Co-relating data – If other data or statistics can be collected using your IP address, a more or less complete profile of any user can be obtained.
Also read:
What is the difference between ethical and unethical tracking?
You will be able to know the difference between malicious and legitimate use by the following aspects:-
- Legitimate Use – In case of legitimate use, web directors use IP grabbing equipment for preventing fraud, analytics, and optimizing content delivery.
- Malicious Use – The attempt is made by hackers for malicious causes when they use IP loggers for tracking users, inflicting attacks, and selling data of users on the black market.
Identifying an IP Grabber

Although there are no telltale signs of an IP grabber, there are certain aspects that you can consider. Let us find out.
- Abbreviated URLs- Be aware of the hyperlinks that are generated from the services that shorten the URLs. These include service providers like Bitly and TinyURL. Also, avoid clicking any link if you are not sure of the identity of the sender.
- Third-party services – Grabify IP logger and other such tools are already known for tracking IP addresses.
- Domains that look suspicious – You might come across URLs that look suspicious and do not carry healthy or useful content.
Protecting yourself from IP loggers
Even if you take utmost care, there might be times when you are not able to identify the threat from Grabify or IP loggers. Note that all IP loggers are malicious. Follow these steps to check it and protect your IP from tracking.
- VirusTotal
You can analyze the hyperlinks for vulnerability.
- CheckShortURL
You can also unmask the shortened links and track their destination.
- Use of VPN
VPN, also known as a Virtual Private Network, helps in masking the real IP address by routing your internet traffic through a stable server. This arrangement makes it almost impossible for the IP grabbers to locate your destination. In this regard, the VPM gateways allow protection and secure the access points, thereby handling encrypted web traffic on the VPN network and the device. These gateways make sure that the connections remain private and safe from external attack.
Some of the commonly used VPNs include the following-
- ExpressVPN
- Surfshark
- NordVPN
- Avoid clicking on unfamiliar links
Even if you think that the link you have received is from someone you know, refrain from clicking on it unless you are certain.
- Keep track of your internet activity.
You can use browser extensions or applications that will send a warning of potential attackers or highlight suspicious links. Two such applications include Privacy Badger and uBlock Origin.
How do Grabify IP loggers use the data obtained?

Hackers or scam artists use different methods to use your data with the help of IP grabbers. The following are the methods-
- Social engineering – Scam artists usually conceal the links and generate links that seem to look like genuine content. When you click on the links, the tool will extract the data and content even without you realising it.
- Example- For instance, a hacker will send a link via email appearing as a bank. This email usually asks for a call-to-action, like verify your account. When you click on the link, the tool grabs your data. Once clicked, the hacker will use the data for future attacks.
- IP Geo targeting – Once they get hold of your IP address, they will develop customised phishing scams.
- Corporate Spying – There are many instances when IP grabbers help to know the details of rivals or market competitors. By phishing or hacking, they will get to know the mode of operation, records, and insights into the rivals’ way of functioning.
Conclusion
Remember, scammers spread most spam links through social media. Platforms like Instagram, Facebook, and Discord are places for creating traps of such links. Scammers hide or embed these links in posts, messages, reviews, and feedback.
You must use tools like Grabify only for legitimate purposes. Stay clear of clickbait and catchy headlines, “win iPhone” and similar titles that tempt users. In a nutshell, you can do the following to stay safe-
- Think twice before you click a link, and also do not click on any link that is from an unknown account.
- Enable link previews. Some systems will allow you to view the links before.
- Stay aware, learn the tips to avoid scammers, and if possible, teach your loved ones to stay alert too.
However, tools like Grabify are not illegal as they have permission to operate. You must exercise greater caution if you are seeing links from unknown sources.
To Get More Updates, Click Here